
SOC 2 Compliance Checklist for 2026: A Practical Guide for CTOs and Security Leaders
Introduction SOC 2 used to be a milestone. You prepared for it once, passed the audit, and moved on. That mindset no longer holds up. In 2026, SOC 2 has
Authentication / Security

Introduction SOC 2 used to be a milestone. You prepared for it once, passed the audit, and moved on. That mindset no longer holds up. In 2026, SOC 2 has

Every IT leader knows this story. Someone forgets a password, calls the help desk, waits for a reset, and loses an hour of productive work. It happens hundreds of times
We live in an API-driven world. From payment systems and healthcare apps to customer portals, everything runs on APIs. But as APIs grow, so do the risks. One insecure connection

Leading organizations understand that identity is the ultimate access control, and to achieve it, biometric authentication is the unbreachable key. Visionary leaders now plug every critical entry point into every

Every login tells a story, but the real question is whether you can trust how it ends. Attackers are no longer breaking in through the front door; they’re walking in

Staring at yet another login screen, trying to recall if the password had an exclamation mark or a number at the end? If that sounds familiar, you’re not alone, it’s
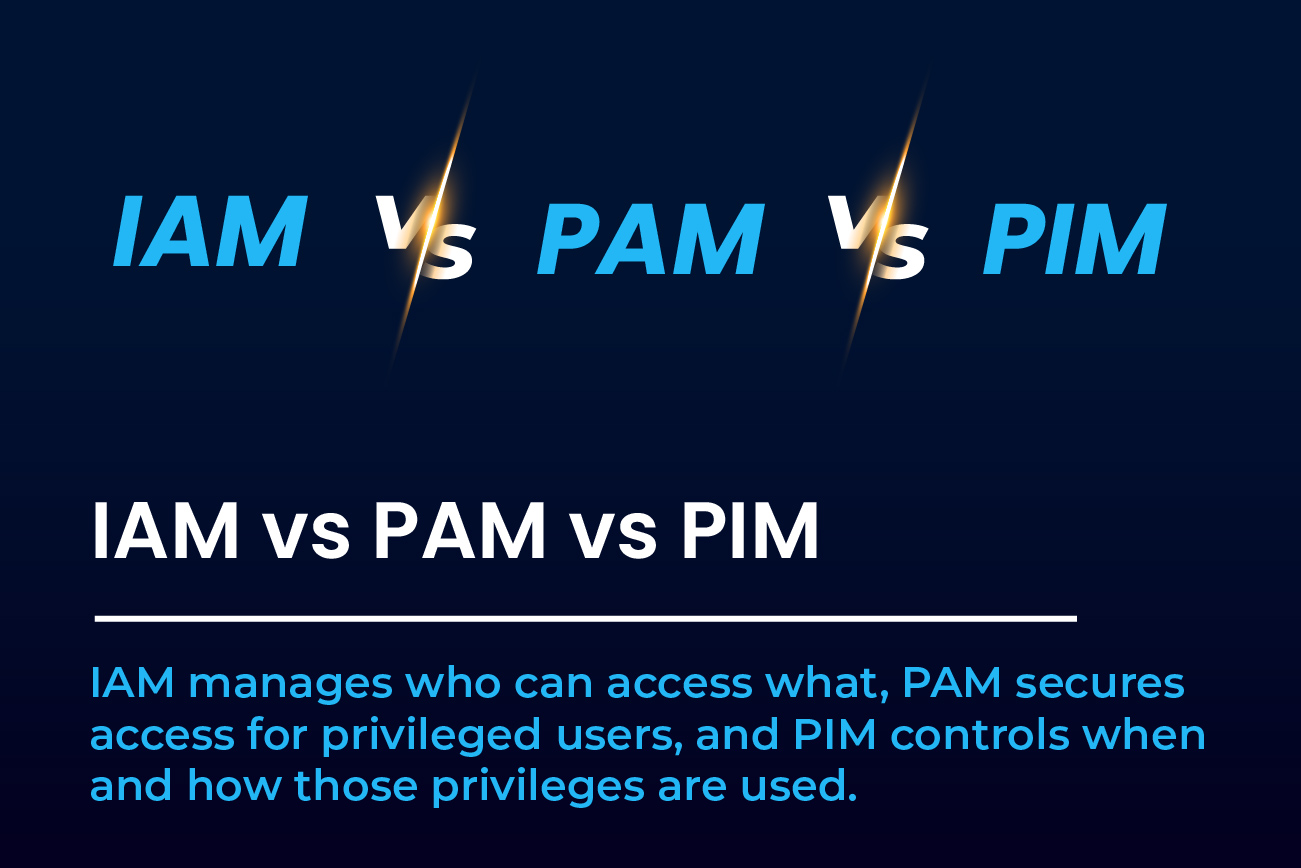
Security acronyms are overwhelming. IAM vs PAM vs PIM might sound like alphabet soup to some, but to security teams, these tools form the backbone of access control and protection.

Why AuthX Believes the Future of Authentication Should Be Effortless and Intent-Aware! We’ve seen this play out a hundred times: A user forgets their password. They reset it. They forget

We’ve seen a lot of changes in cybersecurity over the past decade. But if there’s one thing that’s stayed constant and arguably become even more critical, it’s access control. No

Most conversations around identity security stop at regular users but the real risk often starts with the ones who have the most access. What’s less talked about, yet far more
Join thousands of companies securing their applications with enterprise-grade identity management.
Password managers and Single Sign-On (SSO) both make logging in easier, but they are different tools. Each lets you use one set of credentials to access many applications, which is