
Going Passwordless: 6 Tips to Navigate Passkey Adoption
Passwords were never designed for the digital world we live in today. They were created for much simpler systems, long before attackers had automation, phishing kits, or AI tools that
Authentication / Security

Passwords were never designed for the digital world we live in today. They were created for much simpler systems, long before attackers had automation, phishing kits, or AI tools that

If you’re someone who struggles with messy authentication solutions or worried about keeping user data secure, you’re not alone. Fortunately, JSON Web Tokens better known as JWTs offer a clean,
Long before today’s cloud-ready identity systems, organizations struggled with heavy, complex directory protocols that couldn’t keep up with the fast-growing digital world. That changed in the early 1990s when Tim
Do you know that, despite the rise of modern cloud protocols, roughly 5% of the global Identity & Access Management (IAM) market still relies on Microsoft ADFS, the primary home
Recognizing trusted user devices has become essential today! Whether you’re trying to reduce login friction, improve authentication with two-factor authentication methods, or securely support remote workers. But as more accounts

Password spraying is one of the most insidious types of brute-force password attacks in cybersecurity today. Unlike traditional brute-force methods which bombard a single account with thousands of passwords, a
A dictionary attack is one of the oldest yet most effective password-cracking techniques in cybersecurity. In a dictionary-based attack, hackers use a predefined list of common words, phrases, or passwords
Every IT leader we talk to says the same thing: “We’re tired of chasing passwords.”Finance teams reset them daily. Doctors forget them mid-shift. Factory workers write them on post-it notes.
Every login today represents a choice between convenience and control; a tension that sits at the heart of biometric authentication vs password debates. As security teams, we feel that tension

It’s no secret; most data breaches today don’t start with hackers breaking down digital walls; they start with someone simply logging in using stolen credentials. That’s the reality of shaping
Join thousands of companies securing their applications with enterprise-grade identity management.
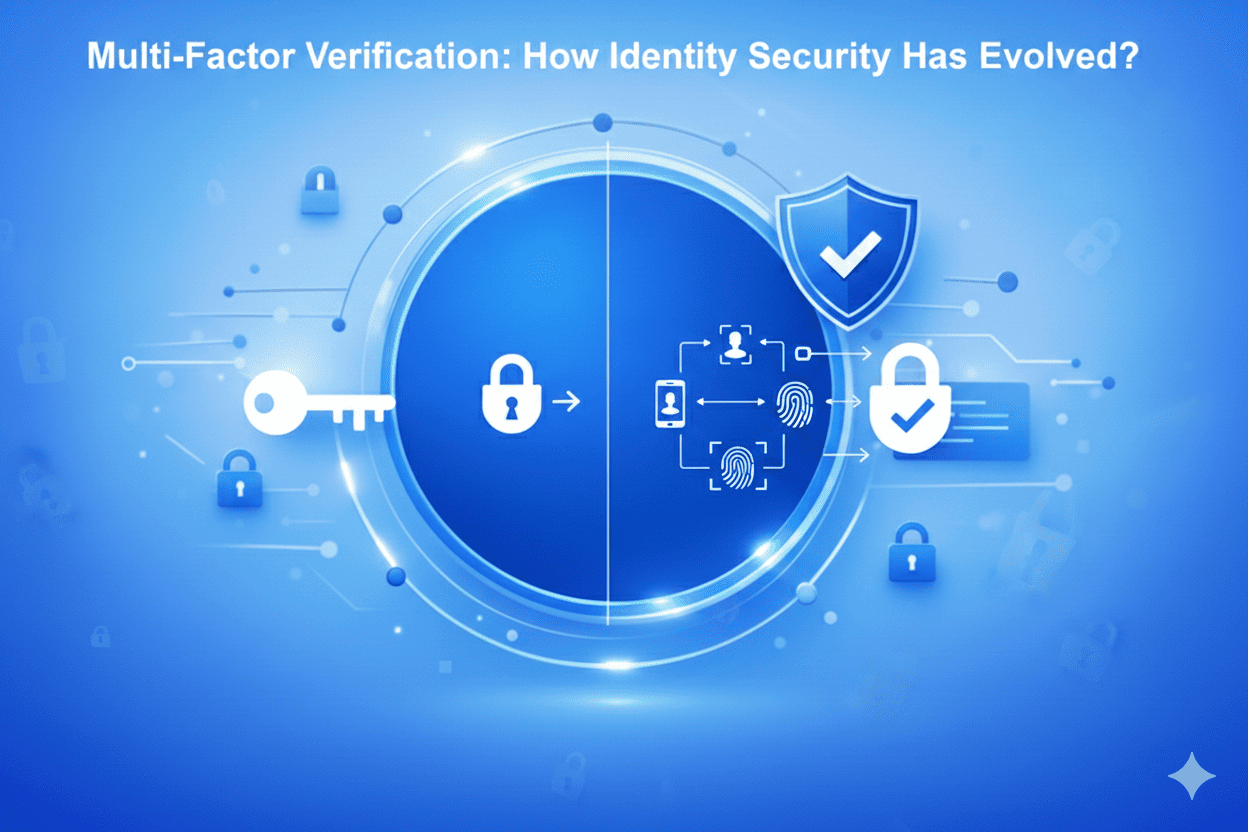
If the last decade taught us anything, it’s that Passwords have aged into one of the weakest links in modern security. We’ve strengthened them, stretched them, wrapped them in complexity,