For years, logging in was simple. You entered a username and password, and that was enough to get access.
But the way we work today looks very different. Employees log in from home, airports, and coffee shops. Contractors and partners access internal systems. Applications run in the cloud, and people use multiple devices throughout the day. At the same time, cyberattacks have become far more sophisticated, with stolen credentials behind a large percentage of data breaches.
This means one thing: a password alone is no longer a reliable way to confirm someone’s identity.
In this beginner-friendly guide, we’ll explore what context-based authentication is, how it works, its key benefits, and how it compares to traditional authentication methods.
What is Context-based Authentication?
Context-based authentication, sometimes also termed as context aware authentication, improves security beyond just using usernames and passwords. Here, it not only checks if a user has the right credentials, but it also looks for real-time risk signals like user behavior, device details, and alerts from other security tools to decide how much to trust each login.
If something looks off, it asks for double authentication, requires identity re-verification, or blocks access. By using context and relying less on static passwords, the risk of unauthorized access and data breaches is greatly reduced.
At its core, context-based authentication works in two steps:
1. Baseline Establishment
To know what unusual behavior is, the system first needs to understand what “normal” looks like for each user. It builds a behavioral profile based on typical locations, devices, and usage patterns.
2. Identifying and Responding to Anomalies
After the baseline is set, the system compares every login attempt to it. It checks for warning signs like logins from unusual locations, risky VPNs, long periods of inactivity followed by odd activity, or compromised devices. If there is any sign of higher risk, it increases security measures, requests additional verification, or blocks access.
How Context-based Authentication Works?
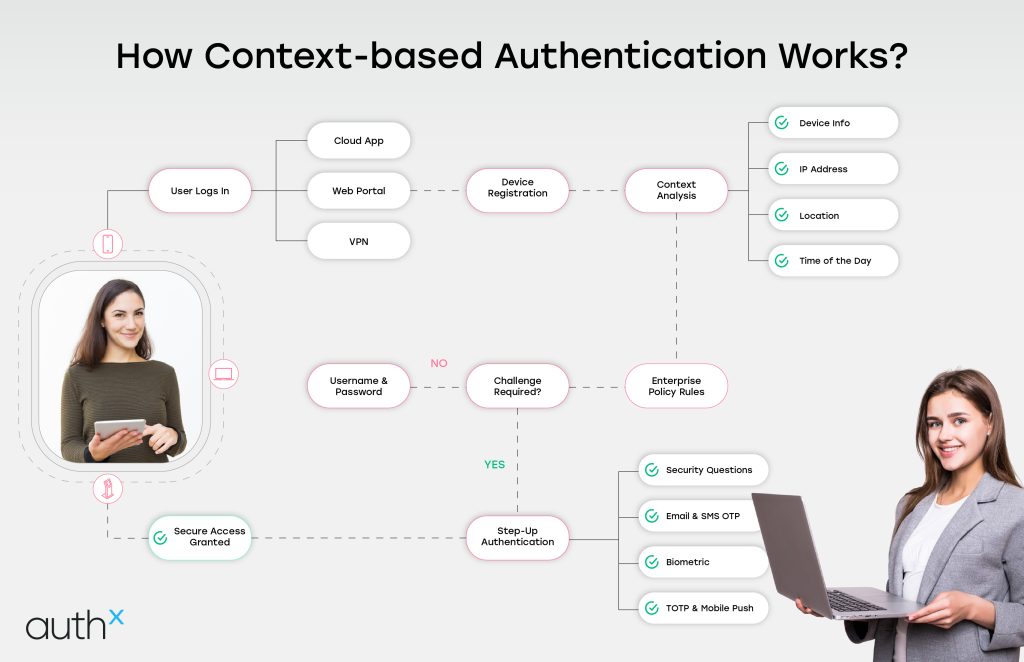
In this section, let’s understand the functioning of Context-based authentication. Context-based authentication starts with collecting important details about each user, such as their usual login times, the devices they use, and the locations they typically sign in from.
With this information, the system creates a unique behavioral profile for each user. When someone tries to log in, the system compares the activity to the user’s usual behavior.
If something is not ordinary, such as a login at an odd time, from a new device, or in another location, the system responds right away. It asks for extra verification or blocks the attempt. This means access is not given just because someone has the password; they also need to act like the real user.
This smart method adds a strong extra layer of protection, making it much harder for unauthorized users to get in.
Key Components of Context-based Authentication
To function effectively, context-based authentication relies on several core components:
1. Context Collection Engine
Collects data from the user, device, network, and environment.
2. Risk Analysis Engine
Evaluates patterns and calculates risk scores based on detection rules and machine-learning models.
3. Policy Engine
Defines what action to take (allow, challenge, deny) based on risk level.
4. Step-Up Authentication
Additional verification methods like OTP, SMS, Biometrics, or Security questions are triggered only when needed.
5. Continuous Monitoring
Keeps evaluating signals throughout the user session; not just at login.
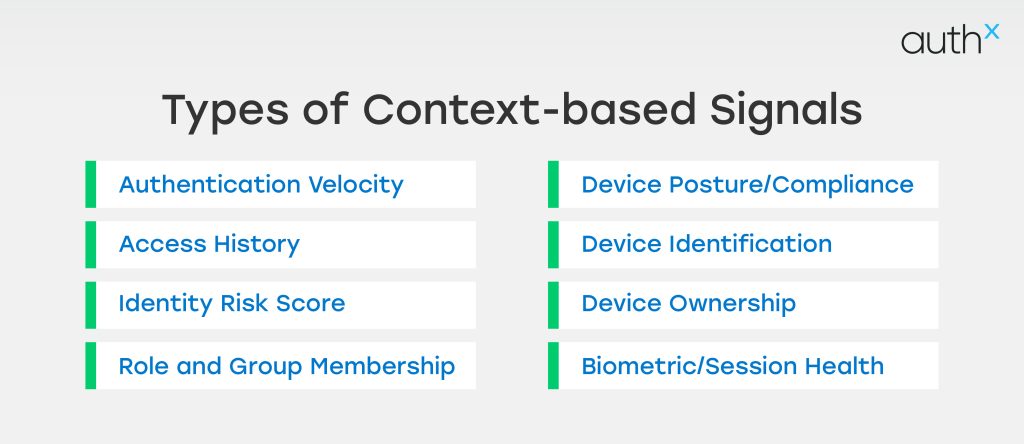
Types of Context Signals Used in Modern IAM
Modern Identity and Access Management (IAM) systems use a variety of risk signals, such as:
Benefits Of Credential Management
| Signal Type |
Description |
IAM Decision Type (Examples) |
|---|---|---|
| Authentication Velocity | Measures the rate and frequency of login attempts (successful or failed). |
Detection: Flagging an account that attempts 10 logins in 5 minutes (potential credential stuffing). |
| Access History |
The user's established pattern of resource access. |
Authorization: If a developer suddenly tries to access HR payroll data for the first time, this is flagged as anomalous. |
| Identity Risk Score |
An aggregated score derived from external sources, such as whether the user’s credentials have appeared in public data breaches. | Policy: If the score is high, force an immediate password reset or deny access. |
| Role and Group Membership | The specific permissions tied to the user's current job function. |
Authorization: Granting access to the "Finance" folder only if the user is in the "Finance Department" group. |
| Device Posture/Compliance | Checks if the device meets security standards (e.g., firewall enabled, antivirus running, operating system is patched). |
Adaptive Access: Only grant full access if the device compliance score is above 90%. |
| Device Identification | Recognizing the specific device based on identifiers (MAC address, unique hardware ID, client certificates). |
Authentication: Allowing a login without MFA only if it comes from a recognized, registered corporate laptop. |
| Device Ownership | Checking if the device is corporate-owned (managed) or personal (unmanaged/BYOD). |
Policy: Limiting data export capabilities only to managed devices. |
| Biometric/Session Health | Continuous checks on user activity during a session (e.g., typing speed, mouse movements, or lack of activity). |
Session Management: Automatically logging out or re-authenticating a user if the session appears hijacked or abandoned. |
Adaptive vs Context-based Authentication
The table below highlights the differences between adaptive authentication and context-based authentication.
| Feature / Criteria |
Adaptive Authentication |
Context-Based Authentication |
|---|---|---|
| Core Concept | Adjusts authentication requirements based on assessed risk levels. | Uses real-time contextual signals to verify identity before granting access. |
| Primary Focus | Dynamic MFA deciding when and how much authentication is needed. | Verifying the legitimacy of the user by analyzing behavior, device, environment, and risk factors. |
| How It Works | Assigns a risk score and increases or decreases authentication friction accordingly. | Builds a behavioral and environmental profile for each user and checks every login against it. |
| Key Signals Used | Risk score, IP reputation, device risk, geolocation, login velocity. | User behavior patterns, device trust, network context, location consistency, geo-velocity. |
| Trigger for Additional Verification | Triggered automatically when risk score surpasses a threshold. | Triggered when context deviates from the user’s established baseline or trusted patterns. |
| Continuous Monitoring | Often event-based (during login). | Continuous, ongoing assessment during login and throughout the session. |
| User Experience | Reduces friction by removing unnecessary MFA in low-risk scenarios. | More seamless, with authentication tailored around user behavior and context. |
| Use Case Strength | Perfect for balancing security and convenience based on dynamic risks. | Ideal for detecting anomalies, preventing account takeovers, and supporting Zero Trust. |
| Examples | Only prompting MFA when a login attempt comes from a new device. | Blocking an attempt from a device behaving unlike the user’s normal usage patterns. |
| Best For | Organizations wanting flexible MFA and lower user friction. | Organizations needing deeper identity intelligence and stronger fraud prevention. |
| Relation to Zero Trust | Supports Zero Trust by adjusting verification based on risk. | Core to Zero Trust because it evaluates identity continuously and contextually. |
| Overall Goal | Right-size security based on present risk. | Ensure the person behind the login is legitimate by understanding their context. |
Benefits of Context-based Authentication
Context-based authentication provides organizations with a modern, intelligent, and risk-aware way to secure access, without slowing users down. Keeping an account of the situation around each login attempt delivers both stronger protection and a far better user experience. Below are a few approaches that help:
1. Security
Context-based authentication looks at multiple real-time signals, such as user behavior, device security, location, and network details. They don’t just rely simply on passwords. This makes it difficult for the attackers to break in using stolen credentials, brute-force methods, or insider threats. Only real users with legitimate behavior gets in.
2. User Experience
Traditional authentication views every login like a potential threat. Context-based authentication doesn’t. When the system sees low risk, such as a familiar device or a typical login pattern, it allows users to sign in with fewer interruptions. This means less friction, fewer MFA prompts, and a faster login experience.
3. Adapts as Your Environment Changes
Context-based authentication acquires the ability to learn and adapt. As a user’s behavior, devices, or work location evolves, the system automatically adjusts. It doesn’t follow rigid rules. It continuously updates risk profiles, making authentication smarter and more effective over time.
4. Compliance
Regulations like GDPR, HIPAA, PCI-DSS, and NIST require strong controls over who can access sensitive data. Context-based, risk-aware access ensures that only verified users can reach protected information. Making it easier for organizations to uphold strict data protection mandates and prove compliance.
5. Supports Zero Trust Strategies
Zero Trust operates on a simple idea: never trust, always verify. Context-based authentication fits perfectly into this model by evaluating every access attempt continuously. It doesn’t assume anyone is safe just because they passed one check. Instead, it verifies the user, device, and risk level every time.
6. Productivity
By only asking for extra verification when it truly matters, context-based authentication keeps the login flow smooth for trusted users. Less friction leads to happier users, fewer help-desk tickets, and improved productivity across the board.
Challenges with Context-based Authentication
While context-based authentication offers better visibility and control than traditional methods, it does come with a few challenges one should be aware of during implementation. Challenges include:
1. Privacy Concerns
Some users may feel uncomfortable about sharing details like their location or device activity. But as there is a saying trust only comes with transparency. A well-defined privacy policy helps ease these concerns by explaining why this data is collected and how it enhances their security.
2. Complexity in Policy Configuration
Setting up contextual rules isn’t always simple. It involves intelligent defaults, careful tuning, and an understanding of multiple technical signals. Many organizations choose to bring in experts or rely on third-party platforms to ensure everything is configured correctly from the start.
3. Integration Overhead
Not every legacy system is built to support contextual authentication signals. Some older applications may need upgrades or additional integration work before you can take full advantage of context-aware security.
How Context-Based Authentication Supports Zero Trust?
Zero Trust is a core cybersecurity approach based on one rule: never trust by default, always verify. Zero Trust demands continuous evaluation of every access attempt rather than depending only on passwords or static checks. This is what context based authentication is designed for.
Context-based authentication makes it easier for organizations to evaluate real-time signals such as user behavior, device type, location, and network conditions before granting access. This adds intelligence and adaptability to the verification process, making it difficult for attackers to slip through. By applying context-based access control, businesses can ensure every request is judged based on risk and not just assumptions.
This approach strengthens overall security and lays the groundwork for achieving key compliance certifications. In the end, context-aware authentication proves to be more than just a feature. It’s a strategic step toward achieving a fully Zero Trust architecture.
Role of AI/ML in Context-Based Authentication
AI-powered context authentication takes identity protection one step higher by using machine learning to learn how users behave in real. It doesn’t simply rely solely on passwords. AI evaluates subtle patterns, typing cadence, navigation behavior, and mouse movements, and uses them to verify identity continuously. This creates a powerful, adaptive layer over traditional authentication solutions.
As AI analyzes ongoing user behavior, it can instantly detect anomalies that may indicate fraud or cyberattacks. A context-aware authentication example might include the system recognizing unusual login speeds, suspicious device characteristics, or unexpected location changes and responding by increasing verification requirements.
A major advantage of AI-driven verification is its use of behavioral biometrics patterns that are incredibly difficult for attackers to imitate. This results in stronger security without slowing users down.
Implement Context-Based Authentication with AuthX
AuthX brings modern security to life by making Passwordless Authentication, device-based authentication the default. Using device-bound security keys and built-in biometrics, AuthX gives users a smooth, low-friction login experience while ensuring high security.
Its adaptive engine pairs real-time risk scoring with clear, customizable policies, meaning your team always knows why access was allowed or denied and can update rules with ease. AuthX processes a wide variety of contextual signals, including device posture, network trust level, geo-velocity, session patterns, and transaction behavior.
This allows organizations to implement true context-based access control, where each login or request is evaluated dynamically. A strong context-based access control example is blocking a login attempt from a trusted account but from an unrecognized device with suspicious network activity.
AuthX integrates seamlessly with existing environments such as SSO platforms, HR systems, and SIEM tools, and offers developer-friendly SDKs to make adding context based authentication to new apps effortless.
Most importantly, AuthX delivers measurable improvements in fewer account takeovers, a smoother user experience, and significantly fewer helpdesk tickets as your organization scales.
FAQs
What is context-based authentication?
Context-based authentication is a security method that evaluates real-time factors such as user behavior, device, location, and network to determine whether an access request should be trusted.
How does context authentication work?
Context authentication works by collecting authentication context signals during each login attempt. These signals may include device health, login time, IP reputation, or user activity patterns.
What role does device-based authentication play in context-based security?
Device based authentication verifies whether a login request comes from a trusted, previously registered device.
What is an example of context-aware authentication?
A simple context-aware authentication example is when a user logs in from their usual device at their workplace and is granted instant access. But if the same user logs in from an unknown device in another country, device-based authentication or MFA is triggered to confirm their identity.
How does context-based access control improve security?
Context based access control improves security by granting or restricting access based on real-time context signals instead of static permissions.
How does contextual authentication differ from traditional methods?
Traditional authentication trusts users once they enter the right password. Contextual authentication continuously analyzes risk using multiple data points.


